Table of Contents
An IT director I know discovered that his company was running 47 applications built by citizen developers. Not in sandboxes. In production. Processing real customer data. Connected to core systems.
IT had no documentation for most of them. No idea who built half of them. Three were created by people who’d left the company months ago. Two were accessing databases they shouldn’t have been able to touch.
His first instinct was to shut everything down. Block the platforms. Reassert control. But he realized that would just drive development even further underground. The business needs that spawned these apps weren’t going away.
That’s the governance challenge with citizen development. You can’t stop it. You can only decide whether it happens where you can see it or where you can’t.
The Control Paradox
Shadow IT exists because official IT processes are too slow or too complicated for what people need. Someone in sales needs a simple tool to track client interactions. IT says it’ll take six months and require three committees to approve.
So they build it themselves using Airtable or Microsoft Power Apps or whatever tool they can access. It works. It solves their problem. They share it with their team. Now you have shadow IT.
Why blocking doesn’t work
The natural IT response is to block these tools. Lock down what people can install. Restrict access to external platforms. Reassert control through prohibition.
This doesn’t stop the behavior. It just makes it less visible. People use personal accounts instead of corporate ones. They use their personal devices. They work around whatever blocks you put in place.
Now you’ve got all the risks of shadow IT plus zero visibility into what’s happening. That’s worse, not better.
The enabling paradox
Here’s the thing nobody wants to admit: citizen developers often deliver faster than IT can. Not necessarily better. Not more secure. Not more maintainable. But faster.
A sales ops person who understands the actual workflow can build a functional tool in a week. IT building the same thing properly takes three months. The fast version ships. People use it. It becomes critical before IT even finishes requirements gathering.
Banning citizen development means accepting that speed. Enabling it means accepting some risk. There’s no option that’s both perfectly safe and perfectly fast.
What Actually Happens Without Governance
Let’s be specific about the problems that emerge when citizen development runs unchecked.
The orphan application problem
Someone builds a tool. It works. People start depending on it. Then the creator leaves the company or changes roles. Nobody else understands how it works. It breaks. Business processes stop.
I’ve seen departments hold on to employees they wanted to let go just because those employees built critical tools nobody else could maintain. That’s a bad position for everyone.
Data access gone wrong
Citizen developers often don’t fully understand data access controls. They connect their app to a database because they need some information. But the connection gives access to way more data than they realize.
Suddenly, HR data is accessible through a sales tool. Financial information is exposed through an operations dashboard. The creator didn’t intend this. They just didn’t understand the implications of the permissions they requested.
Compliance violations
This is where things get expensive. A well-meaning employee builds a tool that processes customer data. They don’t realize it violates GDPR or HIPAA or whatever regulations apply to your business.
Auditors discover it. Now you’ve got a compliance violation that could result in fines, legal issues, and reputational damage. The employee was just trying to help. But ignorance isn’t a defense in regulatory matters.
Integration nightmares
Shadow IT applications often integrate with official systems in ways IT doesn’t know about. When IT updates or changes something, these hidden integrations break. Sometimes spectacularly.
Or worse, they keep working in ways that corrupt data or create inconsistencies between systems. You end up with different versions of truth across your organization.
The Wrong Approach to Control
Before talking about what works, let’s address what doesn’t. Because most organizations start with approaches that make the problem worse.
Requiring approval for everything
Making every citizen development project go through formal IT approval defeats the purpose. You’ve just recreated the slow process that caused shadow IT in the first place.
Citizen development’s value is speed. If getting approval takes weeks, people will just skip the process. You’ve created a policy that ensures non-compliance.
Technical lockdowns
Trying to technically prevent people from using these platforms usually fails. Employees are creative about workarounds. Personal accounts, personal devices, browser-based tools IT can’t block.
You end up in an arms race. IT blocks something. Users find a workaround. IT blocks that. Users find another. Nobody’s actually working on business problems anymore.
Ignoring it entirely
The opposite extreme is equally problematic. Pretending citizen development isn’t happening or that it’s not IT’s problem doesn’t make the risks go away.
Eventually something breaks or causes a compliance issue. Then you’re dealing with consequences rather than preventing them. That’s more expensive and more painful.
Guardrails That Actually Work
Effective governance enables creation while managing risk. It’s about smart constraints, not blanket prohibitions.
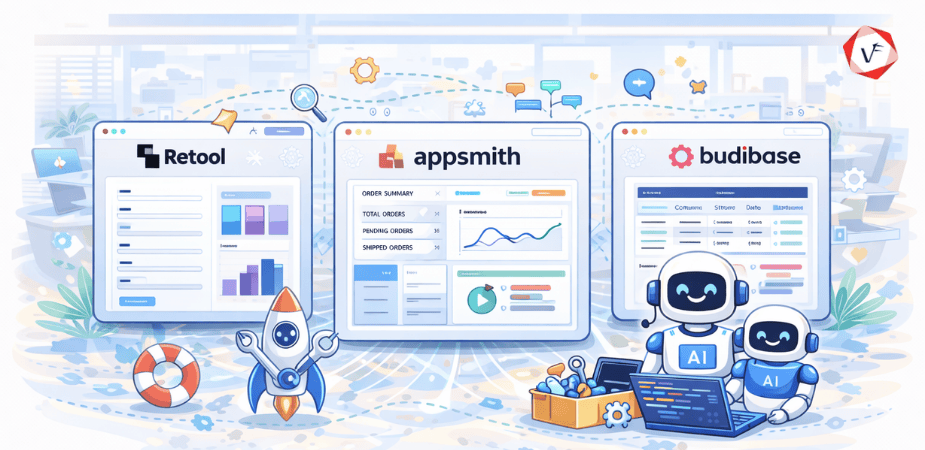
Approved platforms with built-in limits
Provide official low-code platforms. Microsoft Power Platform, Salesforce Lightning, whatever fits your environment. But configure them with guardrails built in.
Data connectors are pre-approved and properly scoped. Users can’t accidentally access HR or financial data. Authentication is centrally managed. Logging is automatic. The platform itself enforces boundaries.
Developers can build freely within these constraints. They don’t need approval for every app. But they also can’t create major security issues because the platform won’t let them.
Automated compliance checks
Instead of manual review, build automated checks that scan citizen-developed applications for common issues:
Does it access sensitive data? Flag for review. Does it integrate with production systems? Require IT verification. Does it process personal information? Ensure proper data handling.
Automation makes compliance scalable. You can check hundreds of apps without hundreds of hours of manual work.
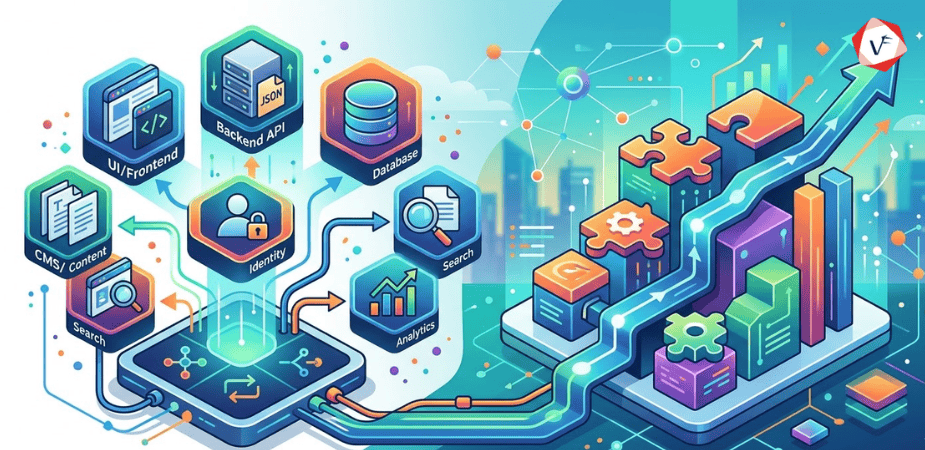
Tiered deployment gates
Different applications need different levels of scrutiny. A personal productivity tool needs minimal oversight. An app processing customer transactions needs a rigorous review.
Development sandbox: fully open, anyone can build anything. Department use: light review, mostly automated checks. Enterprise deployment: formal IT review and security validation. Production with external access: full governance process.
This lets people move fast on low-risk items while maintaining control over high-risk deployments.
Visibility without prohibition
You need to see what’s being built. Application registry, mandatory for anything leaving individual use. Not to approve it, but to know it exists.
Who built it, what data it accesses, what systems it integrates with, and who uses it. This visibility lets you identify risks before they become problems.
Building a Framework That Scales
So, how do you actually implement this? Here’s what works in practice.
Start with approved tools
Pick one or two low-code platforms that fit your environment. Configure them properly. Document what’s allowed and what isn’t. Make training available.
Make the approved path easy. If using sanctioned tools is harder than going rogue, people will go rogue. The official option needs to be the path of least resistance.
Define clear boundaries
What data can citizen developers access? What systems can they integrate with? What requires IT involvement? Make these boundaries explicit and technical where possible.
Don’t rely on people reading policy documents. Build the boundaries into the platforms themselves. Technical controls beat policy compliance every time.
Create a review process for production
Anything moving to production should get IT review. Not to redesign it or tell them they should’ve done it differently. To check for security issues, compliance problems, and integration risks.
Keep the review lightweight. You’re looking for showstoppers, not perfection. Can move to production with recommendations for future improvements.
Build a center of excellence
Create a team that supports citizen developers. They provide training, answer questions, review apps, and help with complex requirements.
This team bridges IT and business. They speak both languages. They help citizen developers stay within guardrails while IT maintains the infrastructure.
The Cultural Shift Required
Governance frameworks are technical, but making them work is cultural. Both IT and business users need mindset changes.
IT shifting from gatekeepers to enablers
Its job isn’t to prevent development. It’s to make safe development possible. That requires a different approach than traditional IT control.
Instead of “no, you can’t build that,” it’s “here’s how to build that safely.” Instead of approval gates, it’s providing platforms with built-in safety.
This is hard for IT teams used to controlling every technical decision. But it’s necessary for governance that actually works.
Citizen developers accepting responsibility
Freedom to build comes with responsibility. Citizen developers need to understand they’re accountable for what they create.
Document your apps. Follow the governance process. Don’t try to work around security controls. If you build something business-critical, you need to support it or hand it off properly.
This responsibility includes knowing when to involve IT. Complex integrations, sensitive data, anything mission-critical, get IT involved early.
Leadership supporting both sides
Executive leadership needs to back the governance framework. That means supporting IT when they enforce boundaries and supporting business users when they need to build quickly.
It’s a balance. Leadership sets the tone by demanding both agility and safety, not choosing one over the other.
When to Intervene
Even with good governance, you’ll encounter situations requiring direct intervention. Knowing when matters.
Clear intervention triggers
Security violations happen immediately. Stop the app, fix the issue, then discuss. Data compliance problems are similar. Legal risk trumps business convenience every time.
Business-critical systems need a formal handoff to IT. When an app becomes essential to operations, it needs proper support. The original creator shouldn’t be solely responsible for something the company depends on.
Gray areas
What about apps that are suboptimal but not dangerous? Apps that work but aren’t well-designed? Apps that solve problems in ways IT wouldn’t choose?
These are judgment calls. If it works and isn’t risky, maybe leave it alone. If it’s causing problems or technical debt is accumulating, have a conversation about better approaches.
The goal isn’t perfect architecture. It’s enabling business value while managing risk.
What Good Governance Actually Achieves
When governance is working, it doesn’t feel like governance. Citizen developers build what they need without feeling restricted. IT maintains visibility and control without becoming a bottleneck.
Shadow IT still exists, but it’s minimal. Because the official path is easier and offers more capability than going rogue. People choose the sanctioned approach not out of compliance fear but because it’s genuinely better.
This takes effort to build. You need the right platforms, clear policies, good training, and a center of excellence to support it. But the alternative is either crushing innovation or accepting uncontrolled risk.
Most companies fall somewhere in the middle. Some shadow IT persists. Some governance is ignored. That’s reality. Perfect compliance isn’t the goal. Managing risk while enabling speed is.
The companies doing this well aren’t the ones with the most restrictive policies. They’re the ones that made safe development easier than unsafe development. That shift in incentives changes everything.
If you’re trying to figure out how to enable citizen development without losing control, or need help building governance frameworks that actually work instead of just existing on paper, Vofox has experience helping companies navigate this balance. We’re not pushing heavy-handed control or unlimited freedom. We’re helping you find the middle ground where business moves fast and IT sleeps at night.